The Risks to Privacy from Collecting and Storing Personal Information


Pretty much every app and website we use collects and stores some of our personal info. Things like your name, location, what you look at, and health data from fitness trackers. It powers things like personalized ads, quick logins, and recommendations that feel right for you. However, the more data companies have, the bigger the target they become, and honestly, a lot of them have more than they actually need. When the company has all your information in one place, it's super easy for someone to access and share without your consent.
The biggest worry is data breaches. This is when hackers sneak in and grab everything. This can lead to identity theft, drained bank accounts, or worse. Even without hackers, lazy setups like leaving databases wide open, or sharing your info with third parties, can expose you without anyone meaning to. Constant tracking through cookies, pixels, and device fingerprints builds detailed profiles about you, which can fuel targeted ads, higher prices, or denied loans. Laws like GDPR in Europe and CCPA in California try to help with this issue, but they're not everywhere.
Some examples include the Equifax breach back in 2017. This event exposed millions of people and caused, not months, but YEARS, of identity theft cases. In 2025, we had events like the PowerSchool hack affecting 62 MILLION students' records, including Social Security numbers! Another was the huge Chinese Surveillance Network leak with billions of records. There were also breaches at places like GrubHub and Discord that leaked names, IDs, and more. Even AI tools can keep sensitive stuff you put in the chat! This is a reminder that "free" services often come with a hidden privacy cost.
How Computing Resources Can Be Misused and How They Can Be Protected


Company computers, networks, servers, and cloud storage are great tools for getting work done. Sadly, people misuse them all the time. For instance, streaming videos or shopping during lunch, however innocent, is a misuse of the tools. This is because it eats up slows things down for everyone who are trying to do real work instead of just watching a video online for the fun of it. Another misuse is when people download sketchy files or go on gambling sites. The really bad stuff includes launching attacks from company resources or spreading malware, which can crash systems, and costs a fortune to fix!
Some solid ways to lock things down are by having stronger firewalls and multi-factor authentication. That way, if someone guesses your password, they're stuck. Add clear rules everyone has to follow, regular training so people know what the risks are, and monitoring while still respecting privacy. Encryption keeps data safe even if it is stolen, and ideas like "least privilege" and zero-trust make it harder to abuse resources.
There have been lots of misuse cases such as employees intentionally or unintentionally leaking files using personal drives or unauthorized apps, which can lead to full-blown breaches. On the other hand, companies that enforce strong passwords, run frequent audits, and use zero-trust setups have lowered things like secret crypto mining or malware sneaking in. Insider misuse is still a problem, but good policies and tech layers make huge differences in keeping everything running smoothly and safely.
How Unauthorized Access to Information Is Gained

Unauthorized access basically means someone gets into systems or data they're not supposed to be in. Hackers use all kinds of methods to break in, and a lot of it starts with tricking people rather than just breaking the code. Phishing emails, texts, or calls that look totally legit trick people into handing over passwords or clicking bad links that drop malware. Weak or reused passwords make guessing or credential stuffing, which is just trying leaked logins from other breaches, all too easy.
Other common methods include exploiting bugs in unpatched software, attacks on open Wi-Fi, or pretending to be IT help to get info. Physical tricks happen too. People can steal a laptop or plug in infected USBs. Once they're inside, attackers often "pivot" to other parts of the network to steal more credentials, or quietly sit there collecting data. In 2025, hackers and scammers have been using AI to phish people, using deepfake voice calls to make scams more convincing.
Examples include phishing that leads to business email compromise, where someone pretends to be the boss and tricks employees into wiring money. There have been huge ransomware waves from exploiting vulnerable VPNs or stolen contractor logins. Credential stuffing from old breaches still hits millions every year, allowing attackers to go from one account to another.
How Computing Innovation Can Be Beneficial and Harmful & Impacts Beyond Intended Purposes
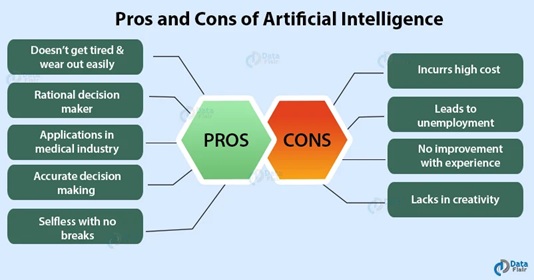

Computing innovations have changed our world for the better in so many ways. Think AI helping doctors spot diseases faster, the internet letting us talk to anyone anywhere. Online classes opening education to people who could never access it before. All of these tools boost creativity, speed up science (like new drug discoveries), and make everyday life more convenient. Telemedicine saved lives during tough times, and machine learning keeps finding patterns humans would miss.
Although these things are good, there's some cons to these tools as well. Automation can wipe out jobs, algorithms sometimes bake in unfair bias (denying loans or jobs to certain groups), and privacy takes a hit when everything tracks you. Social media is built to connect us, but ended up spreading fake news like wildfire, fueling bullying, addiction, and even anxiety or depression for many people. A lot of these downsides go way beyond what the creators planned. GPS was meant for getting around, but now it's used for stalking. AI was built to help but ended up powering deepfakes or mass surveillance.
An example is the World Wide Web. It was invented for sharing research, but it also became a misinformation machine and privacy nightmare. Social platforms promised global friendship but contributed to division, echo chambers, and mental health struggles. In recent years, AI image tools (like Google's Gemini in 2024) spit out wildly inaccurate or biased results, causing backlash. Massive outages from a single bad update (CrowdStrike in 2024) showed how one tiny flaw can cascade into global chaos. These stories show why we need thoughtful design, ethics checks, and rules to get the good without so much of the unexpected harm.